Bitcoin
Bitcoin CPI
Venture Portfolio
Funds
Market Insights
Indicators
About
Contact

April 21, 2026





For a long time, “quantum” has been used as a catch-all phrase to describe a new era of computers that seem to defy understanding, operating at a level once confined to science fiction. In recent years, however, the advent and progress of quantum computing have raised repeated alarms, especially when it comes to high-security systems such as Bitcoin.
This article explains the quantum threat to Bitcoin, how it works, what it means for Bitcoin’s future, and the measures being taken to protect the network from these attack vectors.
Google recently published a whitepaper explaining that future quantum computers may be able to break the cryptography protecting cryptocurrencies with fewer resources than previously realized.
At its core, quantum computing is the ability to perform computations far more quickly than traditional computers by using qubits that rely on the counterintuitive laws of quantum mechanics.
Currently, many internet security systems, including Bitcoin, rely on the assumption that even the most powerful supercomputers would take centuries to break their encryption. Quantum computing could theoretically reduce this to a much shorter timeframe, potentially days or weeks under ideal conditions, making the threat far more realistic.
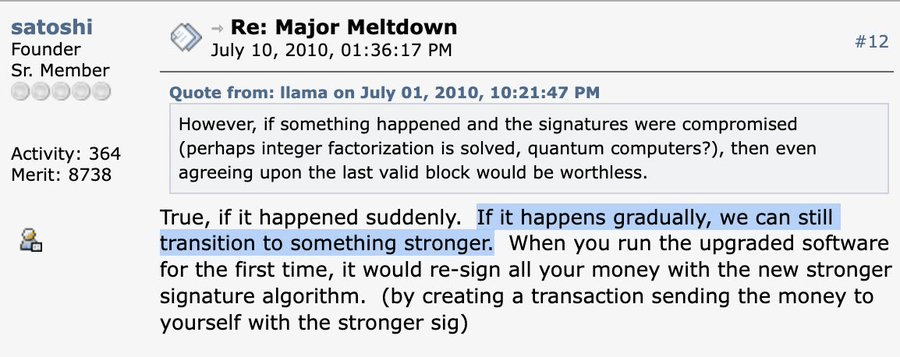
The quantum threat is not new to Bitcoin. Even Satoshi Nakamoto, the pseudonymous creator of Bitcoin, addressed concerns about advancements in quantum computing back in 2010, stating that, “If it happens gradually, we can still transition to something stronger.”
Up until now, though, concerns have been considered largely theoretical, as existing machines were too small to make a meaningful impact. However, Google’s latest research suggests a twenty-fold reduction in the resources necessary to break common types of encryption.
In short, the risk may be closer than previously assumed. In a worst case scenario, some alarmists believe that if Bitcoin’s cryptography were ever fully compromised, confidence could collapse and the price could effectively go close to zero.
Bitcoin’s approach to security is significantly more advanced than, for example, the encryption used by secret messaging apps. The network uses a cryptographic system called Elliptic Curve Digital Signature Algorithm (ECDSA) to prove ownership of funds.
The ECDSA is a variant of public-key cryptography, which at its basis uses a pair of keys: a public key and a corresponding private key. The system’s security depends on you keeping your private key hidden and secure. To sign off a transaction, your private key generates a signature. This signature can be verified against the public key. Neither the signature, nor the public key, can feasibly be used to reverse-engineer your private key.
However, the key word here is ‘feasibly’.
A standard computer is far too slow to even attempt to uncover your private key. Even the fastest supercomputers would need an unimaginable amount of time to attempt it.
Quantum computers, however, can solve certain mathematical problems far more efficiently, making them significantly more capable of undermining the cryptographic security that protects Bitcoin. These systems are known as Cryptographically Relevant Quantum Computers (CRQCs).
Before Google’s research was published, the amount of qubits required to break Bitcoin’s digital signatures was estimated at around 10 million. Recent findings point to a far lower threshold of around 500,000 qubits working together.
Let’s put these numbers into perspective. Currently, Google’s most advanced chip, Willow, has 105 qubits that only stay stable for millionths of a second. For the half a million qubits to be able to break Bitcoin’s cryptography, they would need to be able to stay stable for several minutes.
While this may make it seem like the threat is very far off, Google researchers believe otherwise and have announced a transition to post-quantum cryptography (PQC) with a 2029 deadline.
It’s therefore been widely interpreted that everybody should be on an accelerated path to PQC, in case CRQC development picks up pace in the near future.
It's still worth noting, though, that Google’s research is theoretical and doesn’t take into account factors like error rates, hardware stability, and system design. There are still significant roadblocks to CRQCs, keeping the threat several orders of magnitude beyond today’s reality.
Even with CRQCs likely far off, Bitcoin developers are working on ways to move the network toward post-quantum security. Currently, three major initiatives are focused on keeping Bitcoin secure even in the event of a complete paradigm shift.
The first is BIP 360, a Bitcoin Improvement Proposal that proposes a new output type for Bitcoin. In effect, this would hide your public key until you actually spend, eliminating the quantum-vulnerable keypath exposure. The BIP has been described as “a critical and relatively unobtrusive ‘first step’ in making Bitcoin quantum-resistant.” It’s already merged into Bitcoin's official proposal repository, meaning it’s just a matter of time until it’s live on the mainnet.
The second is SHRINCS, a new signature scheme designed specifically to be small enough to work on Bitcoin. Since most quantum-resistant signatures are huge, SHRINCS is a project making them small (324 bytes, to be precise), with the assumption that your device can keep track of which keys have already been used. In case this doesn’t happen, there’s a fallback mechanism that uses larger signatures to keep you from losing funds.
Finally, the third project is SHRIMPS, which improves upon the single-device SHRINCS by making it available on multiple devices. The signatures resulting from SHRIMPS are typically around 2.5 KB in size, which makes them bigger than SHRINCS, but usable on more than one device at once.
Together, these three projects are targeting the ways in which quantum computing is most commonly expected to be used as an attack vector on Bitcoin. With BIP 360 hiding the addresses until it’s time to spend and SHRINCS plus SHRIMPS introducing quantum-resistant signature schemes, clear steps are already being taken to protect Bitcoin before the threat has even fully materialized.
While Bitcoin developers are working on different ways to make Bitcoin quantum-resistant, there are a few easy anticipatory measures you can take to increase your own security levels.
If your BTC sits in an address that has previously sent a transaction, this public key has been exposed. Any significant risk from quantum computing is negated simply by moving funds to a never-before-used Bitcoin wallet address. This means that users will be strongly encouraged to stop reusing addresses, removing them from the pool of potential targets.
Additionally, wallets, exchanges, and other custody providers are expected to introduce post-quantum solutions as soon as they’re viable. In all likelihood, we’ll have solutions before the problem fully presents itself in the first place.
Ultimately, the quantum threat exists, but is far from imminent. Once the actual quantum breakthrough happens and the computers are truly capable of creating unimaginable opportunities, your Bitcoin will likely already be protected.
Yes, the quantum threat to Bitcoin is real, although it is only theoretical at present. Future quantum computers could potentially break the cryptographic systems that secure the Bitcoin network. However, quantum hardware is far from capable of this currently, and significant technical barriers remain before an attack becomes feasible or likely.
You can reduce your exposure to the potential of quantum attacks by using reputable wallets, avoiding address reuse, and keeping your BTC in addresses that have never been used to send transactions. This prevents your public key from being exposed.